By Dylan Duncan
Cofense Intelligence is monitoring an state-of-the-art marketing campaign that is properly reaching supposed targets in the Oil and Fuel business. The campaign delivers an uncommon, but highly developed, Malware-as-a-Assistance information stealer, the Rhadamanthys Stealer. This new and highly developed phishing campaign employs a just lately up-to-date Malware-as-a-Company (MaaS) within days of legislation enforcement’s takedown of LockBit ransomware team, 1 of the most energetic Ransomware-as-a-Service (RaaS).
Based mostly on a report by Cyberint posted on January 22nd, the malware family members not long ago been given a important update on the black marketplace which could be the rationale we’re observing these types of an unfamiliar family surface in these types of an superior campaign. As of this moment, there are a high quantity of phishing e-mail that employ various tactics, approaches, and strategies identified to support in bypassing secure email gateways to provide the malware.
Breakdown of the Campaign
The marketing campaign begins with a phishing e-mail (Determine 1) working with a motor vehicle incident report to lure victims into interacting with an embedded backlink that abuses an open redirect on a legitimate domain, mainly Google Maps or Google Photos. End users are then redirected several moments just before last but not least achieving an interactive PDF file hosted on a not long ago registered area docptypefinder[.]facts (Figure 2). The PDF is a clickable graphic which reaches out to a GitHub repository and downloads a ZIP archive that incorporates a Rhadamanthys Stealer executable. Once a target makes an attempt to interact with the executable, the malware will unpack and get started a link with a command and manage (C2) locale that collects any stolen credentials, cryptocurrency wallets, or other sensitive info.
Rhadamanthys Stealer is an unheard of but very highly developed Malware-as-a-Assistance that 1st appeared in 2022 and is prepared in the C++ programming language. The stealer implements various attributes to support in its a lot of stealing abilities. The key use for the stealer is for threat actors to steal machine facts, doc information, cryptocurrency wallets, and credentials stored in numerous purposes and browsers. Primarily based on the report by Cyberint the malware a short while ago been given a big update to 5. giving threat actors who purchase the provider a more customizable practical experience and allowing for extra measures to counter stability and exploit vulnerabilities. Desk 1 at the stop of this report reveals a sample of the IOCs pulled from this campaign, and for Cofense customers the comprehensive stack can be viewed on the Energetic Menace Report on ThreatHQ.
We will keep on to present a lot more details when they become available.
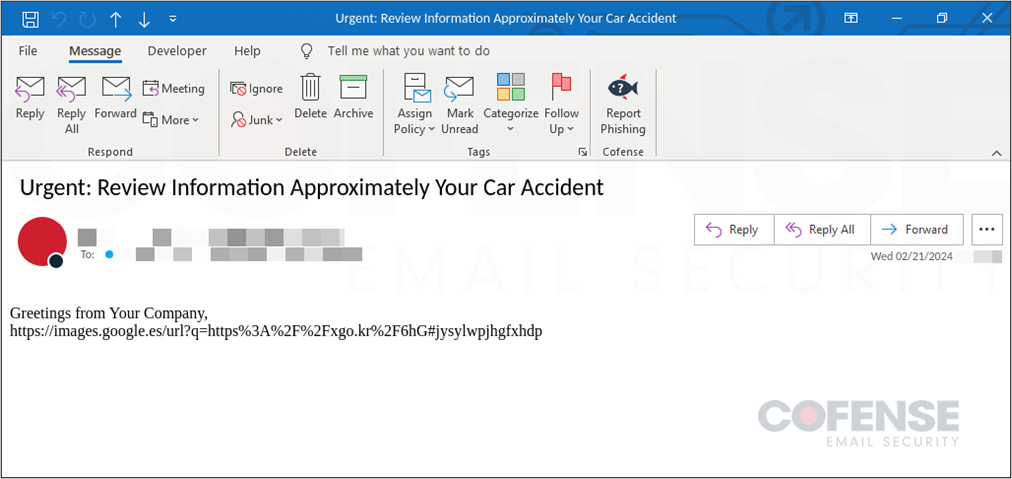
Determine 1: Phishing Electronic mail Focusing on Oil and Gasoline Sector to Supply Rhadamanthys Stealer.
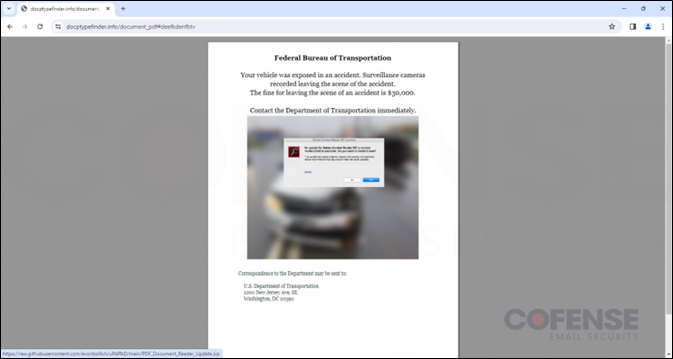
Determine 2: Not too long ago registered area hosting a clickable PDF file.
The publish New MaaS InfoStealer Malware Marketing campaign Focusing on Oil & Gas Sector appeared initial on Cofense.


